Managed cPanel Shared, WordPress and Magento Hosting
Hosting packages optimized for each specific use: Basic Shared cPanel, WordPress & Magento. All fully managed.
-
-
Professional
1 Site Starter cPanel Hosting
$9 Month
- 1 Site
- 500 MB Raid-10 SSD Storage
- 10 GB Tier-1 Data Transfer
- ~40,000 Monthly Visits
-
Business
cPanel Hosting with Extra Resources
$29 Month
- 1 Site
- 50 GB Raid-10 SSD Storage
- 250 GB Tier-1 Data Transfer
- ~1 Million Monthly Visits
-
Enterprise
Enterprise-level cPanel Hosting
$149 Month
- 25 Sites
- 250 GB Raid-10 SSD Storage
- 1 TB Tier-1 Data Transfer
- ~4 Million Monthly Visits
-
-
-
Professional
Hosting for a Single WordPress Site
$19 Month
- 1 Site
- 30GB Raid-10 SSD Storage
- 100GB Tier-1 Data Transfer
- ~500,000 Monthly Visits
-
Business
WordPress Hosting with more Resources
$49 Month
- 5 Sites
- 100GB Raid-10 SSD Storage
- 500GB Tier-1 Data Transfer
- ~2 Million Monthly Visits
-
Enterprise
Hosting for Dozens of WordPress Sites
$239 Month
- 50 Sites
- 500GB Raid-10 SSD Storage
- 2.5TB Tier-1 Data Transfer
- ~10 Million Monthly Visits
-
-
-
Professional
Hosting for Starter Simple Store
$49 Month
- 1 Dedicated IP
- 50GB Raid-10 SSD Storage
- 250GB Tier-1 Data Transfer
- ~100,000 Monthly Visits
-
Business
Ideal for a Larger Magento Store
$89 Month
- 1 Dedicated IP
- 100GB Raid-10 SSD Storage
- 375GB Tier-1 Data Transfer
- ~150,000 Monthly Visits
-
Enterprise
For Enterprise, Advanced-Feature Stores
$189 Month
- 1 Dedicated IP
- 200GB Raid-10 SSD Storage
- 1TB Tier-1 Data Transfer
- ~400,000 Monthly Visits
-
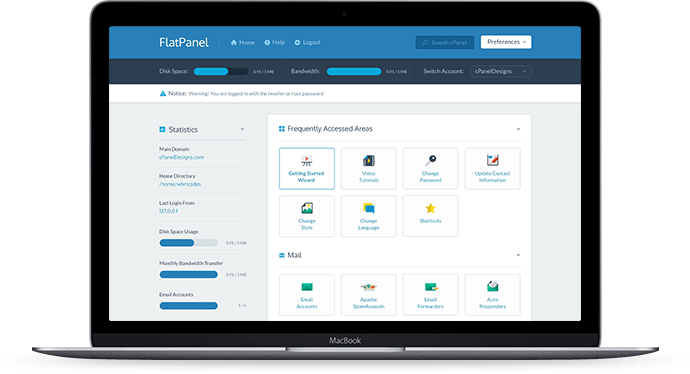
How is T35 different?
T35 Hosting has been a pioneer in the hosting industry since 1997. We have the knowledge and expertise to build reliable and affordable hosting solutions.
All hosting plans come with our premium management to make sure your website is loading the way it should, with no down-time, errors, or issues.
A Web Hosting Company You Can Trust
We’ve been helping customers like you for almost 20 years. We’ve helped pioneer the industry and have perfected the web hosting solutions to help you succeed.
Safe & Secure
We run hardened server software (php suhosin, etc..) to make sure your sites stay safe and secure.
Best Hardware
All of our servers feature the cutting edge in computer hardware with RAID-10 SSD and Quad-Core CPU’s.
Faster Sites
Our tier-1 datacenter is equipped with premium uplinks to make your site load quick around the world.
Managed Support
Our premium managed support team is here to help. No issue is too big, no problem too comlpicated.
Companies Who Trust Our Services
Bullion Exchanges is a trusted and certified Precious Metals Retailer.

Dharma Home Suites is a leading provider of upscale accommodations.
Hootcase is a premium provider of mobile cases & accessories.

Mickey Truck Bodies is one of the leading manufactures of aluminum truck bodies.

SmartSites is New Jersey’s leading online marketing & web development company.

Established in 2002, The Calendar Group is a leading full-service staffing agency.